
Configuring Standard Switch Policies
Learner Objectives
After completing this lesson, you should be able to meet the following objectives:
- Explain how to set the security policies for a standard switch port group
- Explain how to set the traffic shaping policies for a standard switch port group
- Explain how to set the NIC teaming and failover policies for a standard switch port group
Network Switch and Port Policies
Policies that are set at the standard switch level apply to all port groups on the standard switch by default.
Available network policies:
- Security
- Traffic shaping
- NIC teaming and failover
Policy levels:
- Standard switch level: Default policies for all the ports on the standard switch.
- Port group level: Effective policies defined at this level override the default policies that are set at the standard switch level.
Configuring Security Policies
As an administrator, you can define security policies at both the standard switch level and the port group level:
- Promiscuous mode: You can allow a virtual switch or port group to forward all traffic regardless of the destination.
- MAC address changes: You can accept or reject inbound traffic when the MAC address is altered by the guest.
- Forged transmits: You can accept or reject outbound traffic when the MAC address is altered by the guest.

Traffic-Shaping Policies
- Network traffic shaping is a mechanism for limiting a virtual machine’s consumption of available network bandwidth.
- Average rate, peak rate, and burst size are configurable.

Configuring Traffic Shaping
A traffic-shaping policy is defined by average bandwidth, peak bandwidth, and burst size. You can establish a traffic-shaping policy for each port group and each distributed port or distributed port group:
- Traffic shaping is disabled by default.
- Parameters apply to each virtual NIC in the standard switch.
- On a standard switch, traffic shaping controls only outbound traffic, that is, traffic traveling from the VMs to the virtual switch and out onto the physical network.

NIC Teaming and Failover Policies
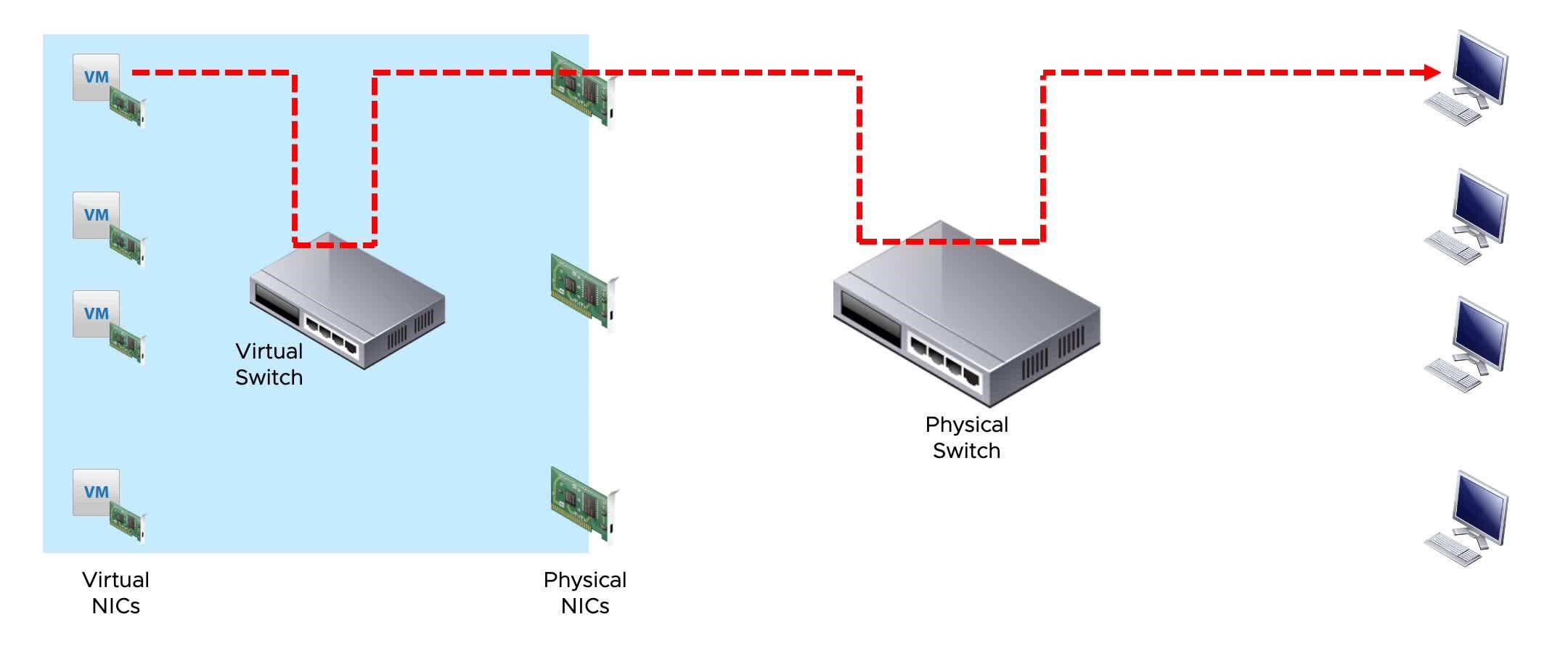
With NIC teaming, you can increase the network capacity of a virtual switch by including two or more physical NICs in a team.

Load-Balancing Method: Originating Virtual Port ID
 With the load-balancing method that is based on the originating virtual port ID, a virtual machine’s outbound traffic is mapped to a specific physical NIC.
With the load-balancing method that is based on the originating virtual port ID, a virtual machine’s outbound traffic is mapped to a specific physical NIC.
Load-Balancing Method: Source MAC Hash
 For the load-balancing method based on source MAC hash, each virtual machine’s outbound traffic is mapped to a specific physical NIC that is based on the virtual NIC’s MAC address.
For the load-balancing method based on source MAC hash, each virtual machine’s outbound traffic is mapped to a specific physical NIC that is based on the virtual NIC’s MAC address.
Load-Balancing Method: Source and Destination IP Hash
 With the IP-based load-balancing method, a NIC for each outbound packet is selected based on its source and destination IP addresses.
With the IP-based load-balancing method, a NIC for each outbound packet is selected based on its source and destination IP addresses.
Detecting and Handling Network Failure
The VMkernel can use link status or beaconing, or both, to detect a network failure.
Network failure is detected by the VMkernel, which monitors the link state and performs beacon probing.
The VMkernel notifies physical switches of changes in the physical location of a MAC address.
Failover is implemented by the VMkernel based on configurable parameters:
- Failback: How the physical adapter is returned to active duty after recovering from failure.
- Load-balancing option: Use explicit failover order. Always use the vmnic uplink at the top of the active adapter list.
Physical Network Considerations
Your virtual networking environment relies on the physical network infrastructure. As a vSphere administrator, you should discuss your vSphere networking needs with your network administration team. The following issues are topics for discussion:
- Number of physical switches
- Network bandwidth required
- Physical switch configuration support for 802.3ad, for NIC teaming
- Physical switch configuration support for 802.1Q, for VLAN tagging
- Physical switch configuration support for Link Aggregation Control Protocol (LACP)
- Network port security
- Link Layer Discovery Protocol (LLDP) and Cisco Discovery Protocol (CDP) and their operation modes, such as listen, broadcast, listen and broadcast, and disabled
Review of Learner Objectives
After completing this Configuring Standard Switch Policies lesson, you should be able to meet the following objectives:
- Explain how to set the security policies for a standard switch port group
- Explain how to set the traffic shaping policies for a standard switch port group
- Explain how to set the NIC teaming and failover policies for a standard switch port group
Key Points
- Virtual switches can have the following connection types: VM port group, VMkernel port, and physical uplinks.
- A standard switch is a virtual switch configuration for a single host.
- Network policies set at the standard switch level can be overridden at the port group level.
- A distributed switch provides centralized management and monitoring for the networking configuration of all ESXi hosts that are associated with the switch.