312-50V10 Practice Test Free – 50 Questions to Test Your Knowledge
Are you preparing for the 312-50V10 certification exam? If so, taking a 312-50V10 practice test free is one of the best ways to assess your knowledge and improve your chances of passing. In this post, we provide 50 free 312-50V10 practice questions designed to help you test your skills and identify areas for improvement.
By taking a free 312-50V10 practice test, you can:
- Familiarize yourself with the exam format and question types
- Identify your strengths and weaknesses
- Gain confidence before the actual exam
50 Free 312-50V10 Practice Questions
Below, you will find 50 free 312-50V10 practice questions to help you prepare for the exam. These questions are designed to reflect the real exam structure and difficulty level.
If an attacker uses the command SELECT*FROM user WHERE name = "˜x' AND userid IS NULL; --"˜; which type of SQL injection attack is the attacker performing?A. End of Line Comment
B. UNION SQL Injection
C. Illegal/Logically Incorrect Query
D. Tautology
Which of the following is the best countermeasure to encrypting ransomwares?A. Use multiple antivirus softwares
B. Keep some generation of off-line backup
C. Analyze the ransomware to get decryption key of encrypted data
D. Pay a ransom
An unauthorized individual enters a building following an employee through the employee entrance after the lunch rush. What type of breach has the individual just performed?A. Reverse Social Engineering
B. Tailgating
C. Piggybacking
D. Announced
What is the purpose of a demilitarized zone on a network?A. To scan all traffic coming through the DMZ to the internal network
B. To only provide direct access to the nodes within the DMZ and protect the network behind it
C. To provide a place to put the honeypot
D. To contain the network devices you wish to protect
You have successfully gained access to a Linux server and would like to ensure that the succeeding outgoing traffic from this server will not be caught by
Network-Based Intrusion Detection Systems (NIDS).
What is the best way to evade the NIDS?A. Out of band signaling
B. Protocol Isolation
C. Encryption
D. Alternate Data Streams
The security administrator of ABC needs to permit Internet traffic in the host 10.0.0.2 and UDP traffic in the host 10.0.0.3. He also needs to permit all FTP traffic to the rest of the network and deny all other traffic. After he applied his ACL configuration in the router, nobody can access to the ftp, and the permitted hosts cannot access the Internet. According to the next configuration, what is happening in the network?
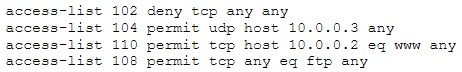
A. The ACL 104 needs to be first because is UDP
B. The ACL 110 needs to be changed to port 80
C. The ACL for FTP must be before the ACL 110
D. The first ACL is denying all TCP traffic and the other ACLs are being ignored by the router
Which of the following is the BEST way to defend against network sniffing?A. Restrict Physical Access to Server Rooms hosting Critical Servers
B. Use Static IP Address
C. Using encryption protocols to secure network communications
D. Register all machines MAC Address in a Centralized Database
PGP, SSL, and IKE are all examples of which type of cryptography?A. Hash Algorithm
B. Digest
C. Secret Key
D. Public Key
Which of the following is considered as one of the most reliable forms of TCP scanning?A. TCP Connect/Full Open Scan
B. Half-open Scan
C. NULL Scan
D. Xmas Scan
_________ is a set of extensions to DNS that provide the origin authentication of DNS data to DNS clients (resolvers) so as to reduce the threat of DNS poisoning, spoofing, and similar types of attacks.A. DNSSEC
B. Resource records
C. Resource transfer
D. Zone transfer
In Wireshark, the packet bytes panes show the data of the current packet in which format?A. Decimal
B. ASCII only
C. Binary
D. Hexadecimal
Which of the following act requires employer's standard national numbers to identify them on standard transactions?A. SOX
B. HIPAA
C. DMCA
D. PCI-DSS
You have gained physical access to a Windows 2008 R2 server which has an accessible disc drive. When you attempt to boot the server and log in, you are unable to guess the password. In your toolkit, you have an Ubuntu 9.10 Linux LiveCD. Which Linux-based tool can change any user's password or activate disabled Windows accounts?A. John the Ripper
B. SET
C. CHNTPW
D. Cain & Abel
You are logged in as a local admin on a Windows 7 system and you need to launch the Computer Management Console from command line.
Which command would you use?A. c:gpedit
B. c:compmgmt.msc
C. c:ncpa.cp
D. c:services.msc
What type of vulnerability/attack is it when the malicious person forces the user's browser to send an authenticated request to a server?A. Cross-site request forgery
B. Cross-site scripting
C. Session hijacking
D. Server side request forgery
Which of the following options represents a conceptual characteristic of an anomaly-based IDS over a signature-based IDS?A. Produces less false positives
B. Can identify unknown attacks
C. Requires vendor updates for a new threat
D. Cannot deal with encrypted network traffic
From the following table, identify the wrong answer in terms of Range (ft).
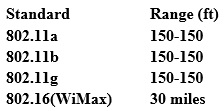
A. 802.11b
B. 802.11g
C. 802.16(WiMax)
D. 802.11a
Sophia travels a lot and worries that her laptop containing confidential documents might be stolen. What is the best protection that will work for her?A. Full Disk encryption
B. BIOS password
C. Hidden folders
D. Password protected files
Which of these is capable of searching for and locating rogue access points?A. HIDS
B. NIDS
C. WISS
D. WIPS
An attacker has installed a RAT on a host. The attacker wants to ensure that when a user attempts to go to "www.MyPersonalBank.com", that the user is directed to a phishing site.
Which file does the attacker need to modify?A. Boot.ini
B. Sudoers
C. Networks
D. Hosts
Insecure direct object reference is a type of vulnerability where the application does not verify if the user is authorized to access the internal object via its name or key.
Suppose a malicious user Rob tries to get access to the account of a benign user Ned.
Which of the following requests best illustrates an attempt to exploit an insecure direct object reference vulnerability?A. "GET/restricted/goldtransfer?to=Rob&from=1 or 1=1' HTTP/1.1Host: westbank.com"
B. "GET/restricted/accounts/?name=Ned HTTP/1.1 Host: westbank.com"
C. "GET/restricted/bank.getaccount("˜Ned') HTTP/1.1 Host: westbank.com"
D. "GET/restricted/rn%00account%00Ned%00access HTTP/1.1 Host: westbank.com"
A company's Web development team has become aware of a certain type of security vulnerability in their Web software. To mitigate the possibility of this vulnerability being exploited, the team wants to modify the software requirements to disallow users from entering HTML as input into their Web application.
What kind of Web application vulnerability likely exists in their software?A. Cross-site scripting vulnerability
B. Web site defacement vulnerability
C. SQL injection vulnerability
D. Cross-site Request Forgery vulnerability
When conducting a penetration test, it is crucial to use all means to get all available information about the target network. One of the ways to do that is by sniffing the network. Which of the following cannot be performed by the passive network sniffing?A. Identifying operating systems, services, protocols and devices
B. Modifying and replaying captured network traffic
C. Collecting unencrypted information about usernames and passwords
D. Capturing a network traffic for further analysis
Which of the following types of jailbreaking allows user-level access but does not allow iboot-level access?A. Bootrom Exploit
B. iBoot Exploit
C. Sandbox Exploit
D. Userland Exploit
If a tester is attempting to ping a target that exists but receives no response or a response that states the destination is unreachable, ICMP may be disabled and the network may be using TCP. Which other option could the tester use to get a response from a host using TCP?A. Traceroute
B. Hping
C. TCP ping
D. Broadcast ping
Which of the following Secure Hashing Algorithm (SHA) produces a 160-bit digest from a message with a maximum length of (264-1) bits and resembles the MD5 algorithm?A. SHA-2
B. SHA-3
C. SHA-1
D. SHA-0
When does the Payment Card Industry Data Security Standard (PCI-DSS) require organizations to perform external and internal penetration testing?A. At least twice a year or after any significant upgrade or modification
B. At least once a year and after any significant upgrade or modification
C. At least once every two years and after any significant upgrade or modification
D. At least once every three years or after any significant upgrade or modification
Which protocol is used for setting up secure channels between two devices, typically in VPNs?A. PPP
B. IPSEC
C. PEM
D. SET
Which one of the following Google advanced search operators allows an attacker to restrict the results to those websites in the given domain?A. [cache:]
B. [site:]
C. [inurl:]
D. [link:]
Which of the following is a serious vulnerability in the popular OpenSSL cryptographic software library? This weakness allows stealing the information protected, under normal conditions, by the SSL/TLS encryption used to secure the Internet.A. SSL/TLS Renegotiation Vulnerability
B. Shellshock
C. Heartbleed Bug
D. POODLE
This asymmetry cipher is based on factoring the product of two large prime numbers.
What cipher is described above?A. SHA
B. RSA
C. MD5
D. RC5
Steve, a scientist who works in a governmental security agency, developed a technological solution to identify people based on walking patterns and implemented this approach to a physical control access.
A camera captures people walking and identifies the individuals using Steve's approach.
After that, people must approximate their RFID badges. Both the identifications are required to open the door.
In this case, we can say:A. Although the approach has two phases, it actually implements just one authentication factor
B. The solution implements the two authentication factors: physical object and physical characteristic
C. The solution will have a high level of false positives
D. Biological motion cannot be used to identify people
Firewalls are the software or hardware systems that are able to control and monitor the traffic coming in and out the target network based on pre-defined set of rules.
Which of the following types of firewalls can protect against SQL injection attacks?A. Data-driven firewall
B. Stateful firewall
C. Packet firewall
D. Web application firewall
What would you enter, if you wanted to perform a stealth scan using Nmap?A. nmap -sU
B. nmap -sS
C. nmap -sM
D. nmap -sT
Code injection is a form of attack in which a malicious user:A. Inserts text into a data field that gets interpreted as code
B. Gets the server to execute arbitrary code using a buffer overflow
C. Inserts additional code into the JavaScript running in the browser
D. Gains access to the codebase on the server and inserts new code
Websites and web portals that provide web services commonly use the Simple Object Access Protocol (SOAP). Which of the following is an incorrect definition or characteristics of the protocol?A. Based on XML
B. Only compatible with the application protocol HTTP
C. Exchanges data between web services
D. Provides a structured model for messaging
The collection of potentially actionable, overt, and publicly available information is known asA. Open-source intelligence
B. Human intelligence
C. Social intelligence
D. Real intelligence
You need a tool that can do network intrusion prevention and intrusion detection, function as a network sniffer, and record network activity. What tool would you most likely select?A. Snort
B. Nmap
C. Cain & Abel
D. Nessus
What is attempting an injection attack on a web server based on responses to True/False questions called?A. DMS-specific SQLi
B. Compound SQLi
C. Blind SQLi
D. Classic SQLi
Bob, your senior colleague, has sent you a mail regarding aa deal with one of the clients. You are requested to accept the offer and you oblige.
After 2 days, Bob denies that he had ever sent a mail.
What do you want to "know" to prove yourself that it was Bob who had send a mail?A. Confidentiality
B. Integrity
C. Non-Repudiation
D. Authentication
You are attempting to run an Nmap port scan on a web server. Which of the following commands would result in a scan of common ports with the least amount of noise in order to evade IDS?A. nmap -A - Pn
B. nmap -sP -p-65535 -T5
C. nmap -sT -O -T0
D. nmap -A --host-timeout 99 -T1
This tool is an 802.11 WEP and WPA-PSK keys cracking program that can recover keys once enough data packets have been captured. It implements the standard FMS attack along with some optimizations like KoreK attacks, as well as the PTW attack, thus making the attack much faster compared to other WEP cracking tools.
Which of the following tools is being described?A. wificracker
B. Airguard
C. WLAN-crack
D. Aircrack-ng
Identify the web application attack where the attackers exploit vulnerabilities in dynamically generated web pages to inject client-side script into web pages viewed by other users.A. SQL injection attack
B. Cross-Site Scripting (XSS)
C. LDAP Injection attack
D. Cross-Site Request Forgery (CSRF)
Bob, a network administrator at BigUniversity, realized that some students are connecting their notebooks in the wired network to have Internet access. In the university campus, there are many Ethernet ports available for professors and authorized visitors but not for students.
He identified this when the IDS alerted for malware activities in the network.
What should Bob do to avoid this problem?A. Disable unused ports in the switches
B. Separate students in a different VLAN
C. Use the 802.1x protocol
D. Ask students to use the wireless network
What is the most common method to exploit the "Bash Bug" or "ShellShock" vulnerability?A. Manipulate format strings in text fields
B. SSH
C. SYN Flood
D. Through Web servers utilizing CGI (Common Gateway Interface) to send a malformed environment variable to a vulnerable Web server
A hacker named Jack is trying to compromise a bank's computer system. He needs to know the operating system of that computer to launch further attacks.
What process would help him?A. Banner Grabbing
B. IDLE/IPID Scanning
C. SSDP Scanning
D. UDP Scanning
What term describes the amount of risk that remains after the vulnerabilities are classified and the countermeasures have been deployed?A. Deferred risk
B. Impact risk
C. Inherent risk
D. Residual risk
Shellshock allowed an unauthorized user to gain access to a server. It affected many Internet-facing services, which OS did it not directly affect?A. Linux
B. Unix
C. OS X
D. Windows
Which Nmap option would you use if you were not concerned about being detected and wanted to perform a very fast scan?A. -T0
B. -T5
C. -O
D. -A
In which of the following cryptography attack methods, the attacker makes a series of interactive queries, choosing subsequent plaintexts based on the information from the previous encryptions?A. Chosen-plaintext attack
B. Ciphertext-only attack
C. Adaptive chosen-plaintext attack
D. Known-plaintext attack
Get More 312-50V10 Practice Questions
If you're looking for more 312-50V10 practice test free questions, click here to access the full 312-50V10 practice test.
We regularly update this page with new practice questions, so be sure to check back frequently.
Good luck with your 312-50V10 certification journey!

