HOTSPOT - A security analyst suspects that a workstation may be beaconing to a command and control server. Inspect the logs from the company's web proxy server and the firewall to determine the best course of action to take in order to neutralize the threat with minimum impact to the organization. INSTRUCTIONS - Modify the Firewall Access Control rule to mitigate the issue. If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.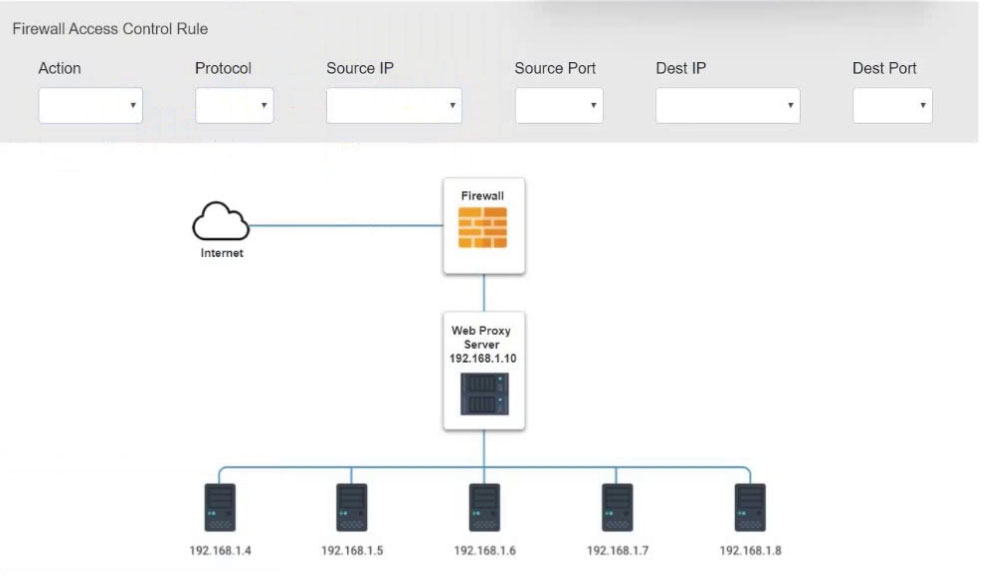

Hot Area:
Suggested Answer:
This question is in CS0-002 CompTIA Cybersecurity Analyst (CySA+) Exam For getting CompTIA Cybersecurity Analyst (CySA+) Certificate Disclaimers: The website is not related to, affiliated with, endorsed or authorized by CompTIA. Trademarks, certification & product names are used for reference only and belong to CompTIA. The website does not contain actual questions and answers from CompTIA's Certification Exams.
Please login or Register to submit your answer

